Intro
The need for organizations to adopt a layered and structured approach to reducing their attack surface is becoming increasingly clear. As enterprise environments expand and become more complex, security teams must adapt to protect their organizations effectively.
One compelling strategy is the implementation of a Continuous Threat Exposure Management (CTEM) program. According to Gartner®, “By 2026, organizations prioritizing their security investments, based on a continuous threat exposure management program, will realize a two-third reduction in breaches.”1
In this blog, we will explore how SixMap aligns with CTEM and can help organizations achieve this critical goal.
CTEM Defined
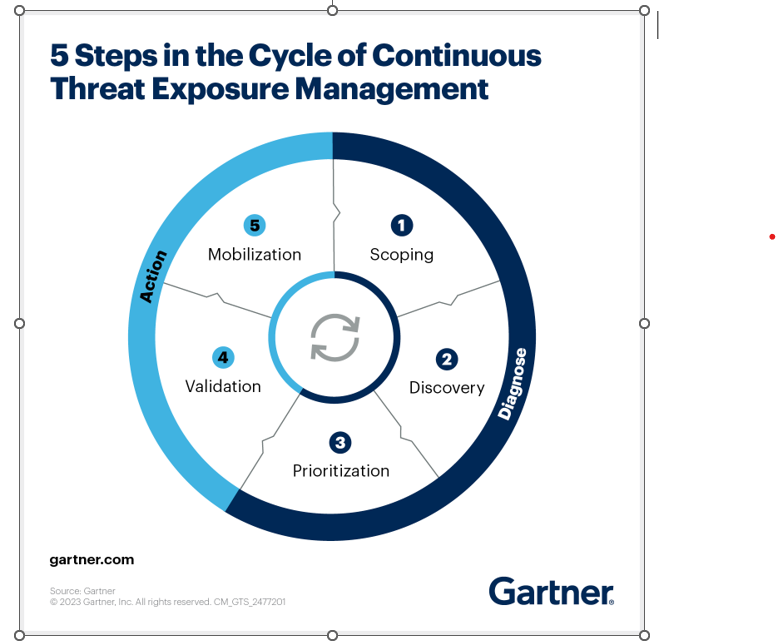
Gartner defines CTEM very clearly, stating “CTEM is a systemic approach to continuously refine cybersecurity optimization priorities. Its objective is to design actionable security exposure remediation and improvement plans that business executives can understand, and that architecture teams can act on. A CTEM cycle includes five stages: scoping, discovery, prioritization, validation and mobilization. Organizations building a CTEM program use tools to inventory and categorize assets and vulnerabilities, and simulate or test attack scenarios and other forms of posture assessment processes and technologies.”
Underscoring the importance of a CTEM approach, Gartner continues by saying “Security vulnerabilities are often one of the main reasons for cybersecurity incidents. Organizations could avoid many of these vulnerabilities with better exposure management. However, decades of using vulnerability assessment tools have shown that even large, well-funded organizations can’t patch every discovered vulnerability.”
Powering CTEM with Automation for Maximum Effectiveness
Unlike traditional vulnerability management programs that typically rely on periodic assessments, successful Continuous Threat Exposure Management requires a relentless process of scanning and analyzing an organization’s Internet-facing assets to identify potential issues and take action before they can be exploited.
The key here is automation, without which security teams will forever fall behind their adversaries. By automating typically manual, repetitive, and time-consuming processes across their CTEM program, organizations can break free of the constant race to catch up with alert backlogs, unpatched vulnerabilities, and looming threats to their external attack surface.
Scoping and Discovery
The first two phases of a CTEM program are at the heart of SixMap’s value to our customers. A SixMap scan of your enterprise will yield a thorough map of your Internet-connected assets across all 65,535 ports on all IP ranges for IPv4 and IPv6, alongside a complete assessment of vulnerabilities in the identified infrastructure. The process is completely automated and only requires your company name.
Validation
Just because a vulnerability exists doesn’t mean attackers can reasonably exploit it. Using the same threat intelligence pulled during the prioritization stage and employing tried-and-true penetration testing measures, SixMap automatically validates that a customer asset is actually exploitable, ensuring that security teams are focused on the threats that matter. Just as important, validation occurs in the customer’s infrastructure, providing practical and actionable results. This departs from some of the more theoretical validation performed in a sandbox environment that may not reflect the customer’s actual environment.
Mobilization
We like to use the term “targeted intelligent action” to describe mobilization. The intelligence built from the previous CTEM steps is used to inform customers exactly what actions will mitigate the security threat.
By extension, organizations should deploy capabilities that give them the option, but not the obligation, to auto-fix vulnerabilities at scale in the mobilization phase of the CTEM process. SixMap examined the concept of automatic remediation in our blog covering the Connectwise Vulnerabilities that affected Change Healthcare.
Take the First Step Toward Automated CTEM
Continuous Threat Exposure Management is not just a tool or a strategy. It is a continuous workflow that prioritizes and addresses the most pressing cybersecurity exposures.
By embracing automation with solutions like SixMap across all phases of the CTEM model, organizations can enhance their defensive capabilities and position themselves to proactively protect against more dynamic and evolving cybersecurity threats. In doing so, they can protect their digital assets and infrastructure and safeguard their reputation and the trust of their stakeholders.
Are you interested in learning more? Request a SixMap demo and learn how to leverage SixMap to automate CTEM within your organization.
1Gartner subscribers can view the entire report, “Top Strategic Technology Trends for 2024: Continuous Threat Exposure Management,” 16 October 2023 at: https://www.gartner.com/en/documents/4840631
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.